security
Smartphone Security: Hurdles and Potential Solutions
The development of smartphone technology is blossoming at the speed of light, especially over the course of the last five years or so,..
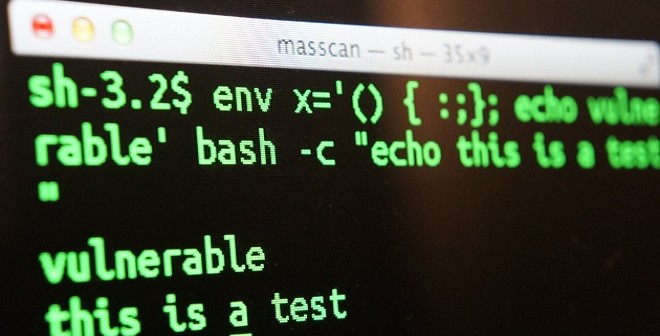
Security Update: Bash Shellshock Vulnerability
NOTE: This article was originally published with the incorrect dates (24th June, instead of 24th September).
On the 24th September 2014 a..
Whitepaper: People’s Role in Cyber Security, an Academics’ Perspective
Cloud Security Considerations for Small Businesses
Even though cloud adoption rates are on the rise and small business owners are not as hesitant to explore the options provided by these..
Whitepaper: Web Hosting Security 2014
Guidelines on How to Handle a Security Breach on Your eCommerce Website
Security breaches are on a constant rise and despite all the time and effort you may have invested into providing a maximum level of..
The Internet of Things and the Emerging Security Questions
If there’s one negative trend that has emerged in unison with life-simplifying technology, it’s that we are more relaxed about who else..
OpenSSL Heartbleed Security Update
On April 7 the OpenSSL Project released an update to address a detected vulnerability (CVE-2014-0160) in their software. OpenSSL is a..
Securing the Australian Cloud: Privacy and Security Requirements for 2014
Cloud technology has entered our lives with a set of new solutions for facilitating our everyday and professional activities on the web,..
Cloud Security: You’re Only as Secure as Your Weakest Link
If you have you been reading the news recently, you might have noticed the spate of high profile security incidents occurring only in the..
Basic Linux VPS Security Measures
Due to virtualisation technology it is easier and cheaper to get a VPS server. Many clients are upgrading their existing Linux shared..
Top 10 WordPress Security Tips
At Crucial we have a large number of customers running their websites on WordPress. Being arguably the most user friendly CMS’ available..